Security questions are insecure how to protect your accounts
Chris Hoffman is Editor-in-Chief of How-To Geek. He’s written about technology for over a decade and was a PCWorld columnist for two years. Chris has written for The New York Times, been interviewed as a technology expert on TV stations like Miami’s NBC 6, and had his work covered by news outlets like the BBC. Since 2011, Chris has written over 2,000 articles that have been read nearly one billion times—and that’s just here at How-To Geek. Read more.
We all know we should create secure passwords. But, for all the time we spend worrying about our passwords, there’s a backdoor we never think about. Security questions are often easy to guess and can often bypass passwords.
Thankfully, many services are realizing security questions are very insecure and axing them. Google and Microsoft no longer offer security questions for their accounts — instead, you can recover an account using an associated phone number.
The Palin “Hack”
This isn’t just a theoretical problem. Sarah Palin’s Yahoo! email account was famously “hacked” in the run-up to the 2008 election. The “hacker” just used the password reset prompt and answered her security question. The question was where she met her spouse, and the answer — Wasilla High — was accessible with a quick Google search.
The Problem With Security Questions
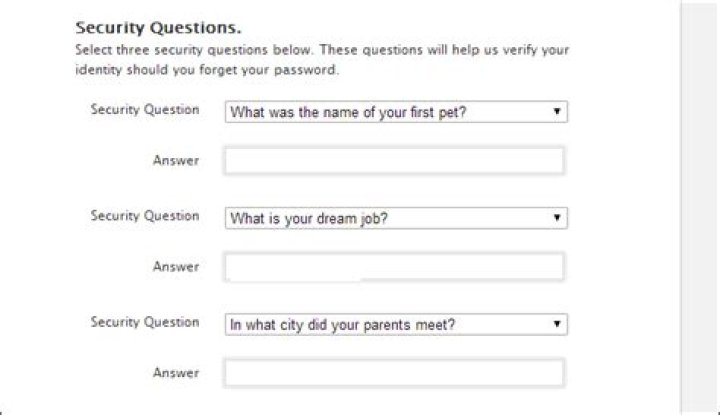
This isn’t just a problem for Sarah Palin. When we set up accounts — from bank accounts to email accounts — we’re often asked to set up a security question. Most of the time, we’ll be provided with a list of suggested questions like “Where did you go to high school?” and “What is your mother’s maiden name?” Some websites allow you to create your own question, but many force you to choose from their list of suggested questions. Some websites force you to set up multiple security questions and answers, which means you can’t just choose a single answer that’s easy to remember — you have to choose several different questions and remember all the answers.
The real problem with security questions is that the answers are so obvious. The answers to many security questions, from “What is your birthday?” to “Where did you go to high school?” are public knowledge, if anyone cares to look. They may even be able to search for them on Google. Even if the answers aren’t public knowledge already, most normal people will share details like where they met their spouse and where they went to school in normal conversation.
Security Question Basics
If you’ve never reset an account’s password, you may never have to deal with your own security questions and may forget about them. You’re often able to click a link that says you forgot your password and, if you answer the security question correctly, you’re given access to that account. In this way, security questions allow you to bypass your password. Your account is no longer as secure as your password is, it’s only as secure as your most obvious security question.
Security question answers are also just easier to guess. For example, if the question is “What was the name of your first pet?”, it’s very easy to guess some common pet names. It doesn’t matter if your password is something as difficult-to-guess as “3&40$d#%$t#kteyt”. If your first pet’s name was “Fido” and you answers the security question accurately, the answer will be easy to guess.
Not every service will reset your account and give someone else access just because they know the answer to your security question, but some will. Other services use security questions as part of an authentication process that will require other personal information.
How to Choose and Answer Security Questions
Keep all this in mind when choosing security questions and answers. Choose something that would be difficult for other people to find out or guess, not something like where you went to school.
The second alternative is to opt out of security questions. For example, if you’re given the chance to write your own security question, you can enter a question like “What is the answer?” or reference an in-joke that only you would know. You can then provide an answer that’s as secure as the question — maybe your answer/question pair is something like “What is the answer?” “45D%po#Yih8d0Y$fgp(i34t”. You now just have a second password for your account — write it down somewhere secure or store it in a password manager like LastPass or KeePass so you can access it in case you ever need it. With an answer like this one, you basically just have a second password.
Bear in mind that you don’t have to answer questions accurately, either. For example, if the question is “Where did you have your first kiss?” and you’ve lived in New York your entire life, you probably don’t want to enter New York — that’s a really obvious answer. Maybe your answer is “In a Crater on the Moon” or another silly response that you’ll remember but other people will have more trouble guessing. Of course, even this answer is more obvious than a seemingly random string. Maybe your answer to “Where did you have your first kiss?” is 9je7%5yry835#9reou&[email protected] Even if you’re forced to use a certain question, you’re free to enter any answer you like as long as you can remember it. Of course, you’ll want to keep this answer safe in case you ever need to provide it in the future.
Security questions are insecure. But, even if you’re forced to use them or forced to use an insecure question, you’re never forced to provide an accurate answer. You can enter any answer you like as long as you can remember it for later. Whatever you do, be sure you aren’t opening a backdoor an attacker could use to bypass your password.
Anyone who has logged into a financial institution’s website in the last few years knows the drill. Enter an ID, a password and then answer a range of questions, ranging from the basic (“What’s your mother’s maiden name?”) to the silly (“What was the name of your favorite stuffed animal?”). Banks and credit card companies put those questions in place as an extra layer of security to protect your accounts and guard against identity theft, but it turns out that they aren’t always effective.
Some questions suffer from the weakness of being easily guessable, like “What color are your eyes?” Others, like “Where did you go to high school?” could be answered by anyone who can look at your social media profiles. For security questions to be truly secure, it’s up to users to create strong answers – or even write their own questions.
In some cases, financial institutions give customers the option to write their own security questions. When doing so, make sure that the questions have answers that are memorable, unchanging, unique and which cannot be easily found online. Examples might be “What was your phone number during third grade?” or “Where did you have your wedding reception?”
If a company doesn’t offer the option for user-created questions, get creative with answers to the existing queries. Try adding special characters (as long as they’re easy to remember), using multiple words or “code” words that give a unique spin to a basic question like “What’s your favorite color?”. The more creative the answer, the less likely it is to be guessed by identity thieves trying to gain access to your accounts.
Weak answers to security questions can leave accounts insecure. Taking the time to create unique answers adds an extra layer of safety and frustrates the efforts hackers, credit card thieves and other scammers.
Chris Hoffman is Editor-in-Chief of How-To Geek. He’s written about technology for over a decade and was a PCWorld columnist for two years. Chris has written for The New York Times, been interviewed as a technology expert on TV stations like Miami’s NBC 6, and had his work covered by news outlets like the BBC. Since 2011, Chris has written over 2,000 articles that have been read nearly one billion times—and that’s just here at How-To Geek. Read more.
Two-factor authentication systems aren’t as foolproof as they seem. An attacker doesn’t actually need your physical authentication token if they can trick your phone company or the secure service itself into letting them in.
Additional authentication is always helpful. Although nothing offers that perfect security we all want, using two-factor authentication puts up more obstacles to attackers who want your stuff.
Your Phone Company is a Weak Link
The two-step authentication systems on many websites work by sending a message to your phone via SMS when someone tries to log in. Even if you use a dedicated app on your phone to generate codes, there’s a good chance your service of choice offers to let people log in by sending an SMS code to your phone. Or, the service may allow you to remove the two-factor authentication protection from your account after confirming you have access to a phone number you configured as a recovery phone number.
This all sounds fine. You have your cell phone, and it has a phone number. It has a physical SIM card inside it that ties it to that phone number with your cell phone provider. It all seems very physical. But, sadly, your phone number isn’t as secure as you think.
If you’ve ever needed to move an existing phone number to a new SIM card after losing your phone or just getting a new one, you’ll know what you can often do it entirely over the phone — or perhaps even online. All an attacker has to do is call your cell phone company’s customer service department and pretend to be you. They’ll need to know what your phone number is and know some personal details about you. These are the kinds of details — for example, credit card number, last four digits of an SSN, and others — that regularly leak in big databases and are used for identity theft. The attacker can try to get your phone number moved to their phone.
There are even easier ways. Or, For example, they can get call forwarding set up on the phone company’s end so that incoming voice calls are forwarded to their phone and don’t reach yours.
Heck, an attacker might not need access to your full phone number. They could gain access to your voice mail, try to log in to websites at 3 a.m., and then grab the verification codes from your voice mailbox. How secure is your phone company’s voice mail system, exactly? How secure is your voice mail PIN — have you even set one? Not everyone has! And, if you have, how much effort would it take for an attacker to get your voice mail PIN reset by calling your phone company?
With Your Phone Number, It’s All Over
Your phone number becomes the weak link, allowing your attacker to remove two-step verification from your account — or receive two-step verification codes — via SMS or voice calls. By the time you realize something is wrong, they can have access to those accounts.
This is a problem for practically every service. Online services don’t want people to lose access to their accounts, so they generally allow you to bypass and remove that two-factor authentication with your phone number. This helps if you’ve had to reset your phone or get a new one and you’ve lost your two-factor authentication codes — but you still have your phone number.
Theoretically, there’s supposed to be a lot of protection here. In reality, you’re dealing with the customer service people at cellular service providers. These systems are often set up for efficiency, and a customer service employee may overlook some of the safeguards faced with a customer who seems angry, impatient, and has what seems like enough information. Your phone company and its customer service department are a weak link in your security.
Protecting your phone number is hard. Realistically, cellular phone companies should provide more safeguards to make this less risky. In reality, you probably want to do something on your own instead of waiting for big corporations to fix their customer service procedures. Some services may allow you to disable recovery or reset via phone numbers and warn against it profusely — but, if it’s a mission-critical system, you may want to choose more secure reset procedures like reset codes you can lock in a bank vault in case you ever need them.
Other Reset Procedures
It’s not just about your phone number, either. Many services allow you to remove that two-factor authentication in other ways if you claim you’ve lost the code and need to log in. As long as you know enough personal details about the account, you may be able to get in.
Try it yourself — go to the service you’ve secured with two-factor authentication and pretend you’ve lost the code. See what it takes to get in. You may have to provide personal details or answer insecure “security questions” in the worst case scenario. It depends on how the service is configured. You may be able to reset it by emailing a link to another email account, in which case that email account may become a weak link. In an ideal situation, you may just need access to a phone number or recovery codes — and, as we’ve seen, the phone number part is a weak link.
Here’s something else scary: It’s not just about bypassing two-step verification. An attacker could try similar tricks to bypass your password entirely. This can work because online services want to ensure people can regain access to their accounts, even if they lose their passwords.
For example, take a look at the Google Account Recovery system. This is a last-ditch option for recovering your account. If you claim to not know any passwords, you’ll eventually be asked for information about your account like when you created it and who you frequently email. An attacker who knows enough about you could theoretically use password-reset procedures like these to get access to your accounts.
We’ve never heard of Google’s Account Recovery process being abused, but Google isn’t the only company with tools like this. They can’t all be entirely foolproof, especially if an attacker knows enough about you.
Whatever the problems, an account with two-step verification set up will always be more secure than the same account without two-step verification. But two-factor authentication is no silver bullet, as we’ve seen with attacks that abuse the biggest weak link: your phone company.
If you’re concerned about the security of your most sensitive online accounts, a physical key serves as a backup to your password for verifying your identity. Here’s how they work.
A password isn’t enough to fully protect your accounts and logins anymore. Websites and apps offer two-factor authentication and biometric login features, but another way to secure your accounts is through a physical security key.
A physical key serves as a backup to your password for verifying your identity. The right type of key can work with your computer and mobile phone, through a physical or wireless connection. Even if someone were to discover the password for one of your accounts, they wouldn’t be able to sign in without the physical key. As long as the key is safe and secure, your private information is protected.
You’ll find a variety of security keys for sale, including ones from Google, Yubico, and Thetis. The key you need depends on your specific needs. If you’re looking to plug it into your computer, choose one with a USB connector. For mobile devices, there are keys with USB-C or Lightning connectors for Android or iOS devices. You may also want one that uses NFC to connect wirelessly, which will cover all your bases and not require you to plug the key in each time.
For this story, I’m using a YubiKey 5C NFC security key from Yubico because of its support for computers and mobile devices. This key has both a USB-C connector and built-in NFC for a wireless connection. Here’s how to use a physical security key to secure your online accounts.
Set Up a Security Key With a Windows PC
One action you might want to take is to secure your Windows 10 login with a security key. In this instance, the key acts as a backup form of authentication beyond your username and password. There is one major limitation here, however. The YubiKey works only with a local Windows account; it won’t work if you use a Microsoft Account to sign into Windows 10. You can have both a Microsoft account and a local account on the computer, but the YubiKey will only log you into the local one.
For this to work, you’ll need to download the Yubico Login for Windows application by clicking on Yubico Login for Windows (64 bit) or Download Yubico Login for Windows (32 bit), depending on your flavor of Windows 10. Install the program and reboot your computer. At the Start menu, open the folder for Yubico and click the shortcut for Login Configuration, then follow the steps in this tool to set up your key.
After your key has been set up, reboot your computer again. At the Windows 10 sign-in screen, make sure your login is set to use the Yubico login in the bottom-left corner of the screen. Enter your Windows 10 username and password. If the YubiKey is not already inserted, you’ll be prompted to insert it and try again. You should then be signed into Windows.
If you run into any trouble configuring the YubiKey, check out the Yubico Login for Windows Configuration Guide.
You can also use the YubiKey as authentication to sign into a variety of websites, and not just those that support the FIDO2 standard. The number of websites that accept physical security keys is limited but always growing. Google supports it, though, so services such as Gmail, Google Calendar, Google Maps, Google Drive, Google Docs, and YouTube will all work with a security key.
Set Up a Security Key With Online Accounts
Open your favorite browser (Chrome, Firefox, and Edge are all supported) and sign into your Google Accounts page. In the left pane, select the setting for Security, then scroll down the page and click 2-step verification. At the next screen, click the Get Started button and sign in with your Google account, if prompted.
Under the Use your phone as your second step to sign in page, click the Show more options link and select Security Key. Click Next, then plug your security key into your computer and click OK. Touch the sensor on the security key to register it, then name your security key if you wish and click Done.
Critical settings so hackers can’t access your bank account USA TODAY
It may seem obvious that you need a strong password to keep hackers from accessing your private information and financial reports. (Photo: Getty Images/iStockphoto)
You need to assume that your password isn’t strong enough. You might as well believe that someone, somewhere, is working around the clock to break into your accounts and steal your money, your identity and anything else you have. Because it’s essentially true.
Maybe you’ve taken precautions. You use security software. You have set up your router’s security so hackers cannot access every device on your network, get your passwords or use your systems as a bot in their attacks.
After you do that, you’re far from done. Hackers are smart and always on the move.
Here are five simple solutions to protect your business, your nest egg and your future.
Don’t make these common mistakes with passwords
It may seem obvious that you need a strong password to keep hackers from accessing your private information and financial reports. Millions of people are sitting ducks because of insecure passwords like 12345678 or Password. They also use the same password for multiple sites.
The ground rules for passwords are: 1) It has to contain a random collection of letters (uppercase and lowercase), numbers and symbols; 2) It has to be eight characters or longer; and 3) You have to create a unique password for every account.
That’s a tall order. While something like “Tl|_|,BwwB2R” is really strong, it isn’t easy to remember. Or is it? Let me show you how I came up with it.
Start by thinking up a random sentence. You can use a catchphrase, quote or even a song lyric. I chose a lyric from a Bruce Springsteen song: “Tramps like us, baby we were born to run.”
I took the first character from each word to get “tlu,bwwbtr”. Not bad, but it could be better. So, I added some symbols in place of similar letters. U becomes |_|, the “to” from the original lyric becomes 2. Then, I capitalized a few of the letters to make a strong password that I can easily remember: “Tl|_|,BwwB2R”.
Once you have that you can tweak the same password for multiple accounts. For Facebook, you could make it “Tl|_|$,BwwB2RFB.” Amazon can be “AmzTl|_|$,BwwB2R.” You can make a consistent scheme.
To prevent criminals from opening bank, utility and phone accounts in your name, you need more than a credit freeze. Here’s what to do. USA TODAY
Make it harder for hackers to crack the code
Hackers can quickly figure out your password, but they can’t figure out the secret, one-time code that your bank texts to you. Two-factor authentication (2FA) is a powerful security method because hackers would have to physically steal your phone, enter the correct password, and then enter that secret code.
In the wake of large-scale hacks, most major accounts offer two-factor authentication, from social media to banks.
Keep track of all your pennies
Most of us have at least one bank account (and often more) plus credit accounts, PayPal and other depositories for our money. These can be hard to keep track of, especially when you have additional investments and personal savings goals.
It’s easier to keep track of your business finances if all these accounts are aggregated in one place, right in front of your eyes.
These days that means an app like Intuit’s Mint. The Mint app, and others like it, can help you set budgets and manage your bills. You can also get reminders to pay bills when they’re due.
Know your credit score
Your credit score will tell you a lot about hackers. If you see anything suspicious on them, like credit card accounts that you didn’t open, you can alert whichever credit bureau is reporting it, whether it’s Experian, Equifax or TransUnion.
Of course, it’s easier than ever to check your credit report. You can check free sites like the Discover credit card site, which says, “You don’t have to be our customer, and there’s no ding to your credit.”
The important thing is to check your credit reports. You should start with the three credit bureaus, each of which gives you one free credit report every year.
Freeze your credit
You may have heard financial advisers telling people to freeze their credit. But you may not know why they’re suggesting that.
Here’s a simple overview. Hackers will have a tough time accessing your personal information if you’ve asked the credit bureaus to freeze your credit – you can’t access it, either, unless you ask them to unfreeze it.
The federal government starting this year mandates that you can freeze your credit for free by calling the three credit bureaus, Experian, Equifax and TransUnion. They have to freeze your credit within one business day of you requesting the freeze by phone or on their websites.
What digital lifestyle questions do you have? Call my national radio show and click here to find it on your local radio station. You can listen to the Kim Komando Show on your phone, tablet or computer. From buying advice to digital life issues, click here for my free podcasts.
If you’re concerned about the security of your most sensitive online accounts, a physical key serves as a backup to your password for verifying your identity. Here’s how they work.
A password isn’t enough to fully protect your accounts and logins anymore. Websites and apps offer two-factor authentication and biometric login features, but another way to secure your accounts is through a physical security key.
A physical key serves as a backup to your password for verifying your identity. The right type of key can work with your computer and mobile phone, through a physical or wireless connection. Even if someone were to discover the password for one of your accounts, they wouldn’t be able to sign in without the physical key. As long as the key is safe and secure, your private information is protected.
You’ll find a variety of security keys for sale, including ones from Google, Yubico, and Thetis. The key you need depends on your specific needs. If you’re looking to plug it into your computer, choose one with a USB connector. For mobile devices, there are keys with USB-C or Lightning connectors for Android or iOS devices. You may also want one that uses NFC to connect wirelessly, which will cover all your bases and not require you to plug the key in each time.
For this story, I’m using a YubiKey 5C NFC security key from Yubico because of its support for computers and mobile devices. This key has both a USB-C connector and built-in NFC for a wireless connection. Here’s how to use a physical security key to secure your online accounts.
Set Up a Security Key With a Windows PC
One action you might want to take is to secure your Windows 10 login with a security key. In this instance, the key acts as a backup form of authentication beyond your username and password. There is one major limitation here, however. The YubiKey works only with a local Windows account; it won’t work if you use a Microsoft Account to sign into Windows 10. You can have both a Microsoft account and a local account on the computer, but the YubiKey will only log you into the local one.
For this to work, you’ll need to download the Yubico Login for Windows application by clicking on Yubico Login for Windows (64 bit) or Download Yubico Login for Windows (32 bit), depending on your flavor of Windows 10. Install the program and reboot your computer. At the Start menu, open the folder for Yubico and click the shortcut for Login Configuration, then follow the steps in this tool to set up your key.
After your key has been set up, reboot your computer again. At the Windows 10 sign-in screen, make sure your login is set to use the Yubico login in the bottom-left corner of the screen. Enter your Windows 10 username and password. If the YubiKey is not already inserted, you’ll be prompted to insert it and try again. You should then be signed into Windows.
If you run into any trouble configuring the YubiKey, check out the Yubico Login for Windows Configuration Guide.
You can also use the YubiKey as authentication to sign into a variety of websites, and not just those that support the FIDO2 standard. The number of websites that accept physical security keys is limited but always growing. Google supports it, though, so services such as Gmail, Google Calendar, Google Maps, Google Drive, Google Docs, and YouTube will all work with a security key.
Set Up a Security Key With Online Accounts
Open your favorite browser (Chrome, Firefox, and Edge are all supported) and sign into your Google Accounts page. In the left pane, select the setting for Security, then scroll down the page and click 2-step verification. At the next screen, click the Get Started button and sign in with your Google account, if prompted.
Under the Use your phone as your second step to sign in page, click the Show more options link and select Security Key. Click Next, then plug your security key into your computer and click OK. Touch the sensor on the security key to register it, then name your security key if you wish and click Done.
The next time you need to sign into your Google account, make sure the security key is inserted in your computer. When you enter your username and password, you will be prompted to touch the key to authenticate your login. You can then use the same security key in any browser and on any computer to sign into your account.
Set Up a Security Key With a Mobile Device
To use a Yubico security key for login authentications on your phone, you first need to download and install the Yubico Authenticator app (iOS, Android) on your device. Open the app and follow the steps to connect the YubiKey to your phone using USB, Lightning, or wireless NFC.
You can now use your Yubico security key to sign into supported apps and websites with your phone. Yubico has a database of websites and applications that are compatible with YubiKey, which you can use to set up your existing accounts with increased security. Click on a supported website, such as Twitter, and select the Get Setup Instructions button.
On your phone, sign into the Twitter website. Go to Settings and Privacy > Security and account access > Security > Two-factor authentication. You’ll first have to set up authentication through either text message or authentication app. Once this is set, check the box next to Security Key.
Plug in your security key or hold it at the top of your phone. Create a PIN or password to secure this login method. You should then receive a message telling you that you’re all set. The next time you try to sign into mobile Twitter, enter your username and password and then plug in or hold your security key next to your phone to authenticate your account.
Share:
- Click to share on Twitter (Opens in new window)
- Click to share on Facebook (Opens in new window)
- Click to share on Pinterest (Opens in new window)
You need to assume that your passwords aren’t strong enough. You might as well believe that someone, somewhere, is working around the clock to break into your accounts and steal your money, your identity and anything else you have. Because it’s essentially true.
Maybe you’ve taken precautions. You use security software. If you don’t, tap or click here for three free downloads for optimum Windows security.
You have set up your router’s security so hackers cannot access every device on your network, get your passwords, or use your systems as a bot in their attacks. To be sure, tap or click here for five router security settings to turn on before it’s too late. After you do that, you’re far from done. Hackers are smart and always on the move.
Here are five simple solutions for you to protect your online bank accounts.
1. Don’t make these common mistakes with passwords
It may seem obvious that you need a strong password to keep hackers from accessing your private information and financial reports. Millions of people are sitting ducks because of insecure passwords like 12345678 or Password. They also use the same password for multiple sites.
The ground rules for passwords are 1. It has to contain a random collection of letters (uppercase and lowercase), numbers and symbols; 2. It has to be eight characters or longer; and 3. You have to create a unique password for every account.
That’s a tall order. While something like “Tl|_|,BwwB2R” is really strong, it isn’t easy to remember. Or is it? Let us show you how we came up with it.
Start by thinking up a random sentence. You can use a catchphrase, quote, or even a song lyric. We chose a lyric from a Bruce Springsteen song: “Tramps like us, baby we were born to run.”
We took the first character from each word to get “tlu,bwwbtr.” Not bad, but it could be better. So, we added some symbols in place of similar letters. U becomes |_|, the “to” from the original lyric becomes 2. Then, we capitalized a few of the letters to make a strong password that I can easily remember: “Tl|_|,BwwB2R”.
Once you have that you can tweak the same password for multiple accounts. For Facebook, you could make it “Tl|_|,BwwB2RFB.” Amazon can be “AmzTl|_|,BwwB2R.” You can make a consistent scheme. Tap or click here for more help creating stronger passwords.
2. Make it harder for hackers to crack the code
Hackers can quickly figure out your password, but they can’t figure out the secret, one-time code that your bank texts to you. Two-factor authentication (2FA) is a powerful security method because hackers would have to physically steal your phone, enter the correct password and then enter that secret code.
In the wake of large-scale hacks, most major accounts offer two-factor authentication, from social media to banks. If you’re not sure how to set up 2FA on your accounts, we have your back. Tap or click here for the steps to get it done on your most popular accounts targeted by hackers.
3. Keep track of all your pennies
Most of us have at least one bank account (and often more) plus credit accounts, PayPal, and other depositories for our money. These can be hard to keep track of, especially when you have additional investments and personal savings goals.
It’s easier to keep track of your business finances if all these accounts are in aggregated in one place, right in front of your eyes.
These days, that means an app like Intuit’s Mint. The Mint app, and others like it, can help you set budgets and manage your bills. You can also get reminders to pay bills when they’re due.
4. Know your credit score
Your credit score will tell you a lot about hackers. If you see anything suspicious on them, like credit card accounts that you didn’t open, you can alert whichever credit bureau is reporting it, whether it’s Experian, Equifax, or TransUnion.
Of course, it’s easier than ever to check your credit report. You can check free sites like the Discover credit card site, which says, “You don’t have to be our customer, and there’s no ding to your credit.”
The important thing is to check your credit reports. You should start with the three credit bureaus, each of which gives you one free credit report every year. Tap or click here to find out how to check your credit for free.
5. Freeze your credit
You may have heard financial advisers telling people to freeze their credit. But you may not know why they’re suggesting that.
Here’s a simple overview. Hackers will have a tough time accessing your personal information if you’ve asked the credit bureaus to freeze your credit —- you can’t access it, either, unless you ask them to unfreeze it.
The federal government mandates that you can freeze your credit for free by calling the three credit bureaus, Experian, Equifax, and TransUnion. They have to freeze your credit within one business day of you requesting the freeze by phone or on their websites.
To help you out, we have the steps to freeze your credit on our site. Tap or click this link to get started now.
Since cybercriminals are always coming up with new scams and better tools, nothing is 100% secure. But, incorporating these simple security settings will help safeguard your online bank accounts and give you a fighting chance.
If you’re concerned about the security of your most sensitive online accounts, a physical key serves as a backup to your password for verifying your identity. Here’s how they work.
A password isn’t enough to fully protect your accounts and logins anymore. Websites and apps offer two-factor authentication and biometric login features, but another way to secure your accounts is through a physical security key.
A physical key serves as a backup to your password for verifying your identity. The right type of key can work with your computer and mobile phone, through a physical or wireless connection. Even if someone were to discover the password for one of your accounts, they wouldn’t be able to sign in without the physical key. As long as the key is safe and secure, your private information is protected.
You’ll find a variety of security keys for sale, including ones from Google, Yubico, and Thetis. The key you need depends on your specific needs. If you’re looking to plug it into your computer, choose one with a USB connector. For mobile devices, there are keys with USB-C or Lightning connectors for Android or iOS devices. You may also want one that uses NFC to connect wirelessly, which will cover all your bases and not require you to plug the key in each time.
For this story, I’m using a YubiKey 5C NFC security key from Yubico because of its support for computers and mobile devices. This key has both a USB-C connector and built-in NFC for a wireless connection. Here’s how to use a physical security key to secure your online accounts.
Set Up a Security Key With a Windows PC
One action you might want to take is to secure your Windows 10 login with a security key. In this instance, the key acts as a backup form of authentication beyond your username and password. There is one major limitation here, however. The YubiKey works only with a local Windows account; it won’t work if you use a Microsoft Account to sign into Windows 10. You can have both a Microsoft account and a local account on the computer, but the YubiKey will only log you into the local one.
For this to work, you’ll need to download the Yubico Login for Windows application by clicking on Yubico Login for Windows (64 bit) or Download Yubico Login for Windows (32 bit), depending on your flavor of Windows 10. Install the program and reboot your computer. At the Start menu, open the folder for Yubico and click the shortcut for Login Configuration, then follow the steps in this tool to set up your key.
After your key has been set up, reboot your computer again. At the Windows 10 sign-in screen, make sure your login is set to use the Yubico login in the bottom-left corner of the screen. Enter your Windows 10 username and password. If the YubiKey is not already inserted, you’ll be prompted to insert it and try again. You should then be signed into Windows.
If you run into any trouble configuring the YubiKey, check out the Yubico Login for Windows Configuration Guide.
You can also use the YubiKey as authentication to sign into a variety of websites, and not just those that support the FIDO2 standard. The number of websites that accept physical security keys is limited but always growing. Google supports it, though, so services such as Gmail, Google Calendar, Google Maps, Google Drive, Google Docs, and YouTube will all work with a security key.
Set Up a Security Key With Online Accounts
Open your favorite browser (Chrome, Firefox, and Edge are all supported) and sign into your Google Accounts page. In the left pane, select the setting for Security, then scroll down the page and click 2-step verification. At the next screen, click the Get Started button and sign in with your Google account, if prompted.
Under the Use your phone as your second step to sign in page, click the Show more options link and select Security Key. Click Next, then plug your security key into your computer and click OK. Touch the sensor on the security key to register it, then name your security key if you wish and click Done.
The next time you need to sign into your Google account, make sure the security key is inserted in your computer. When you enter your username and password, you will be prompted to touch the key to authenticate your login. You can then use the same security key in any browser and on any computer to sign into your account.
Set Up a Security Key With a Mobile Device
To use a Yubico security key for login authentications on your phone, you first need to download and install the Yubico Authenticator app (iOS, Android) on your device. Open the app and follow the steps to connect the YubiKey to your phone using USB, Lightning, or wireless NFC.
You can now use your Yubico security key to sign into supported apps and websites with your phone. Yubico has a database of websites and applications that are compatible with YubiKey, which you can use to set up your existing accounts with increased security. Click on a supported website, such as Twitter, and select the Get Setup Instructions button.
On your phone, sign into the Twitter website. Go to Settings and Privacy > Security and account access > Security > Two-factor authentication. You’ll first have to set up authentication through either text message or authentication app. Once this is set, check the box next to Security Key.
Plug in your security key or hold it at the top of your phone. Create a PIN or password to secure this login method. You should then receive a message telling you that you’re all set. The next time you try to sign into mobile Twitter, enter your username and password and then plug in or hold your security key next to your phone to authenticate your account.
With technology increasingly present in our lives, ensuring the security of your company’s information has become a must. The market offers numerous tools to prevent cyberattacks and control internal access to sensitive data. One of the most efficient solutions we have is Privileged Access Management – PAM.
See below some of the most common questions when looking for a practical and really efficient solution to protect your company:
What Are Privileged Accounts?
All the time, malicious people appear looking for flaws within the companies’ systems to gain access to confidential data. This threat can be both external and internal. Therefore, organizations are increasingly looking for solutions that are truly capable of protecting this information.
Privileged accounts are created to control access to this data. This access is usually restricted only to people who hold leadership positions (high-level management) and administrators in the IT area. Other employees can obtain this information with the authorization of the company.
Although it is extremely important, proper control often ends up being flawed. Because of that, there is this need to have a tool really capable of directing, tracking, and filtering these accesses. Among the most efficient, we have PAM solutions.
Why Should I Invest in a PAM Solution?
Lack of control over access to certain data within an enterprise can result in major disruptions, including loss of business continuity. Many adopted systems end up vulnerable due to a lack of effective supervision.
This lack of control leaves room for the leak of information, much of it sensitive, inside or outside the company. But after all, how to guarantee the privacy of these contents?
The PAM solutions turn out to be quite efficient in this case, as they use security strategies and technologies that, together, are capable of controlling privileged access.
Moreover, they restrict which users will be allowed to enter certain accounts, applications, devices, processes, and internal systems, and control them. This prevents external attacks, which can occur as a result of an employee’s lack of attention, or sharing of sensitive information within the company.
To better understand how this management is done, we made a post explaining everything about PAM solutions.
Are PAM Solutions Really Secure?
We often associate external attacks as our only risk. However, insider threats can also put an entire organization at risk.
They are not always associated only with the people who work in a company. In this list, we can also include service providers, such as consultants, third parties and suppliers, and even former employees, who may have access to its data even after leaving the company.
Improper access can result in damage caused intentionally or accidentally. No matter the reason, in all cases the consequences can be quite bad and even irreversible.
Therefore, it is common for people to have doubts whether a PAM solution is capable of filtering these people’s access. And the answer to that question is yes! It is so secure that they are recommended by cybersecurity experts. Gartner, for example, has chosen PAM as the number-1 security project for 2 years in a row.
When it comes to reducing risk within an organization, a PAM solution is considered one of the most efficient and indispensable. It is worth mentioning that it is always important to hire credible solutions from the market.
senhasegura, for example, offers really efficient solutions, which protect the customer from possible data theft, in addition to tracking the actions of administrators on networks, servers, databases, and devices. All of this is done in compliance with demanding global standards such as ISO 27001, PCI DSS, HIPAA, and Sarbanes-Oxley.
How Does it Reduce Insider Threats?
The PAM solution uses some features to mitigate insider and external threats. One is by protecting the credentials of your most confidential data in a central, secure vault to which few people (with permission) have access.
Privileged access can be limited so that only authorized people can consult personal customer data, trade secrets, ongoing negotiations, intellectual property, financial data, among others.
Privileged Access Management is able to direct which access each employee will have authorization. Thus, they will only be able to consult information relevant to their tasks. All of this will be controlled by the system, no matter if they are working in person or remotely.
In addition to internal data, in order to have greater control over protection against attacks, it is also possible to restrict access to external content on websites and applications that pose a certain type of threat to a company’s security.
Is It Possible to Protect My Passwords in The Cloud?
Yes. senhasegura is the only company in Brazil that offers a cloud-native password vault. The SaaS service protects your credentials, offers password rotation, auditing, and monitoring of these privileged accounts.
In this way, you minimize the duties of the security administrative department and allow the process to take place efficiently and at a lower cost. Therefore, it is ideal for small and medium-sized companies due to its advantages.
Is PAM The Same Thing As IAM?
No. Although both have the principle of controlling a company’s data, the two usually work in a complementary way, each with its own functionality.
In comparison, we can say that PAM is a little more elaborate. Identity and Access Management (IAM) is a tool used for administrators to easily manage users and legitimize access to certain company resources.
Despite that, this type of system has some gaps when it comes to privileged accounts. It is at this point that PAM becomes essential, as it works in a broader and more detailed way. This solution can inform you of everything that is being done, which sessions were started, and who is accessing certain information.
In short, a PAM solution controls everything related to this data within the company, managing to filter accessibility and ensure secure storage of all information.
Do you have any more questions on the subject? Get in touch with the senhasegura team, as we can help you find the ideal product for your needs.
Ensuring your company’s security does not have to be a concern anymore. We are sure of that, as we are experts when it comes to PAM Solution. Visit our website and learn more about all our products and services.