How to knock into your network
We’ve shown you how to trigger WOL remotely by “Port Knocking” on your router. In this article, we will show how to use it to protect a VPN service.
Preface
If you’ve used DD-WRT’s built in functionality for VPN or, have another VPN server in your network, you might appreciate the ability to protect it from brute force attacks by hiding it behind a knock sequence. By doing this, you will filter out the script kiddies that are trying to gain access to your network. With that said, as stated in the previous article, port knocking is not a replacement for a good password and/or security policy. Do remember that with enough patience an attacker can discover the sequence and perform a replay attack.
Also keep in mind, that the downside of implementing this is that when any VPN client/s want to connect, they would have to trigger the knock sequence beforehand and that if they can’t complete the sequence for any reason, they will not be able to VPN at all.
Overview
In order to protect *the VPN service we will first disable all possible communication with it by blocking the instantiating port of 1723. To achieve this goal, we will use iptables. This is because, that is how communication is filtered on most modern Linux/GNU distributions in general and on DD-WRT in particular. If you’d like more information about iptables checkout its wiki entry, and have a look at our previous article on the subject. Once the service is protected, we will create a knock sequence that would temporarily open the VPN instantiating port and also automatically close it after a configured amount of time, while keeping the already established VPN session connected.
Note: In this guide, we are using the PPTP VPN service as an example. With that said, the same method can be used for other VPN types, you’ll just have to change the blocked port and/or communication type.
Prerequisites, Assumptions & Recommendations
- It is assumed/required that you have an Opkg enabled DD-WRT router.
- It is assumed/required that you have already performed the steps in the “How To Knock Into Your Network (DD-WRT)” guide.
- Some networking knowledge is assumed.
Lets get cracking.
Default “Block new VPNs” rule on DD-WRT
While the below snippet of “code” would probably work on every, self-respecting, iptables using, Linux/GNU distribution, because there are so many variants out there we will only show how to use it on DD-WRT. Nothing is stopping you, if you wish, from implementing it directly on the VPN box. However, how to do so, is beyond the scope of this guide.
Because we want to augment the router’s Firewall, it is only logical that we would add to the “Firewall” script. Doing so, would cause the iptables command to be executed every time the firewall is refreshed and thus keeping our augmentation in place for keeps.
From DD-WRT’s Web-GUI:
- Go to “Administration” -> “Commands”.
- Enter the below “code” into the text-box:
inline=”$( iptables -L INPUT -n | grep -n “state RELATED,ESTABLISHED” | awk -F : )”; inline=$(($inline-2+1)); iptables -I INPUT “$inline” -p tcp –dport 1723 -j DROP
What is this “Voodoo” command?
The above “voodoo magic” command does the following:
- Finds where is the iptable line that enables already established communication to pass through. We do this, because A. On DD-WRT routers, if the VPN service is enabled, it will be located just below this line and B. It is essential to our goal of continuing to allow already established VPN sessions to live on after the knocking event.
- Deducts two (2) from the output of the listing command to account for the offset caused by the informational column headers. Once that’s done, adds one (1) to the above number, so that the rule that we are inserting will come just after the rule that allows already established communication. I’ve left this very simple “math problem” in here, just to make the logic of “why one needs to reduce one from the rule’s place instead of adding one to it” clear.
KnockD configuration
We need to create a new triggering sequence that will enable new VPN connections to be created. To do this, edit the knockd.conf file by issuing in a terminal:
Append to the existing configuration:
[enable-VPN]
sequence = 02,02,02,01,01,01,2010,2010,2010
seq_timeout = 60
start_command = iptables -I INPUT 1 -s %IP% -p tcp –dport 1723 -j ACCEPT
cmd_timeout = 20
stop_command = iptables -D INPUT -s %IP% -p tcp –dport 1723 -j ACCEPT
This configuration will:
- Set the window of opportunity to complete the sequence, to 60 seconds. (It’s recommended to keep this as short as possible)
- Listen to a sequence of three knocks on ports 2, 1 and 2010 (this order is deliberate to throw ports scanners off track).
- Once the sequence has been detected, execute the “start_command”. This “iptables” command will place an “accept traffic destined to port 1723 from where the knocks came from” on the top of the firewall rules. (The %IP% directive is treated specially by KnockD and is replaced with the IP of the knocks origin).
- Wait for 20 seconds before issuing the “stop_command”.
- Execute the “stop_command”. Where this “iptables” command does the reverse of the above and deletes the rule that allows communication.
Author‘s tips
While you should be all set, there are a couple of points that i feel need mentioning.
- Troubleshooting. Remember that if you’re having problems, the “troubleshooting” segment at the end of the first article should be your first stop.
- If you want, you can have the “start/stop” directives execute multiple commands by seperating them with a semi-colen (;) or even a script. Doing so will enable you to do some nifty stuff. For example, I have knockd send me an *Email telling me that a sequence has been triggered and from where.
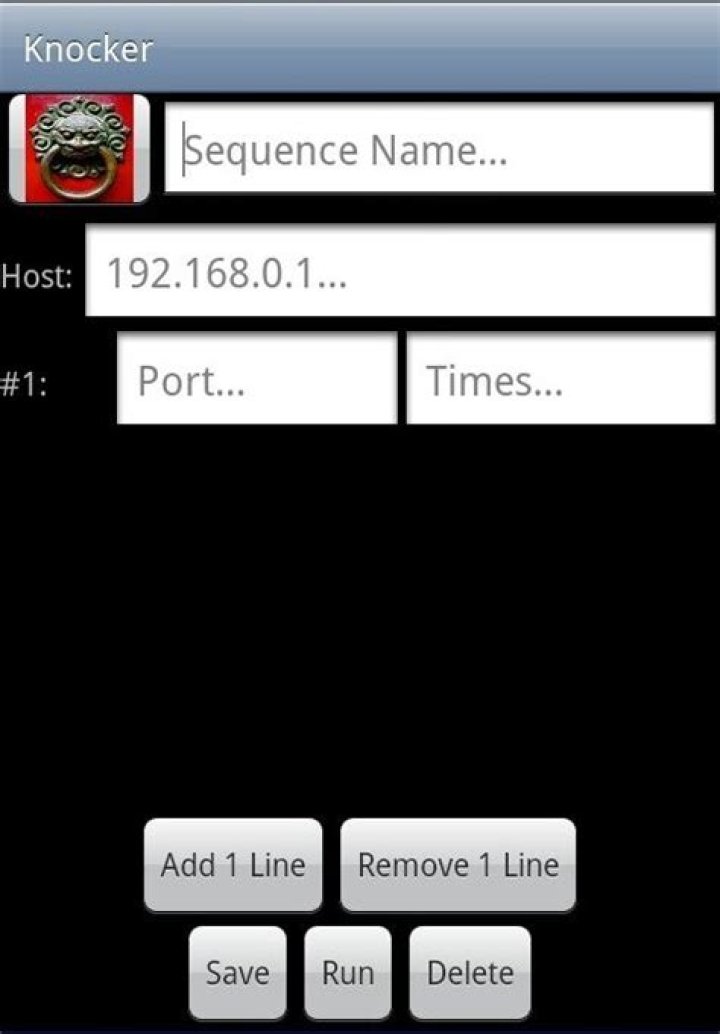
- Don’t forget that “There’s an app for that” and even though its not mentioned in this article, you are encouraged to grab StavFX‘s Android knocker program.
- While on the subject of Android, don’t forget that there is a PPTP VPN client usually built into the OS from the manufacturer.
- The method of, blocking something initially and then continuing to allow already established communication, can be used on practically any TCP based communication. In fact in the Knockd on DD-WRT 1
6 movies, I’ve done way back when, I’ve used the remote desktop protocol (RDP) which uses port 3389 as an example.
Last Updated: November 25, 2020 References Tested
This article was co-authored by Luigi Oppido. Luigi Oppido is the Owner and Operator of Pleasure Point Computers in Santa Cruz, California. Luigi has over 25 years of experience in general computer repair, data recovery, virus removal, and upgrades. He is also the host of the Computer Man Show! broadcasted on KSCO covering central California.
The wikiHow Tech Team also followed the article’s instructions and verified that they work.
This article has been viewed 430,753 times.
This wikiHow teaches you how to kick an unwanted guest off of your Wi-Fi network. Booting someone off of a network is possible on most router configuration pages, though the experience of doing so varies heavily depending on the router. You can also use an application called “NetCut” to remove intruders from your network if you have a Windows computer. If all else fails, resetting your router to factory settings will remove unwanted connections.
I edited this screenshot of a Windows icon.\n
I edited this screenshot of a Windows icon.\n
I edited this screenshot of a Mac icon.\n
Luigi Oppido
Computer & Tech Specialist Expert Interview. 13 November 2020. If prompted, enter the login username and password. If you didn’t set these credentials yourself, you’ll probably find them on the back of the router, in the router’s manual, or in the router’s online documentation.
- You may be prompted to log in later when you attempt to change your router’s settings.
Luigi Oppido
Computer & Tech Specialist Expert Interview. 13 November 2020. Most router pages have a section where they list all current connections by name. This section will usually be labeled Wi-Fi Connections, Connected Devices, or something similar.
- For some routers, you’ll have to find the Parental Controls section instead.
L et’s consider the situation, you have forgotten the password of your WiFi Network Or you are in Office or in your Friends house and don’t know the password of available WiFi Network. So, in these cases how to connect to locked WiFi without password?
Also Read:
Here you will get the simple trick, how to get into someone WiFi without going through the authentication process. This article is for educational purpose only. Don’t use these trick for doing any illegal activities.
Yes, you can connect to locked WiFi Without password by using the functionality of WPS (WiFi Protected Set Up). Most of the Routers support WPS function. For this trick, you must have physical access to the Router of WiFi network you want to connect to. If you are on Windows or Android device, then you are lucky, this trick will gonna work for you. Because Apple Ecosystem doesn’t support the WPS function.
Disclaimer & Strict Warning: This article is only for educational purpose. Don’t use the information given in this article to do anything illegal. If you break or violate any Law, our website and author will not be responsible for any actions taken against you.
What is WPS & How It Works?
WPS stands for WiFi Protected SetUp and it allows you to make connections between wireless devices without selecting the Network Name & entering the password. Now, the question arises, Why this functionality of WPS required? There are various wireless devices like Wireless Printer or Wireless Repeater in which we can not enter password. Here WPS makes things much easier & faster.
In this case, to connect our smartphone with WiFi network, we will on WPS on both Router and Smartphone simultaneously. And your smartphone will get connected to the Wifi network of this router automatically within some seconds.
How To Connect To Locked WiFi Without Password
Now you must have got the little idea about WPS & its functionality. So, Let’s apply this trick to connect to locked WiFi without password. Steps are very straightforward & simple. just follow the steps given below and also Watch 2 min Step by Step Live Video Tutorial:
Step 1: Go to “Settings” in your Smartphone –> “WiFi” –> Go to “More” or “3 Vertical dot icon” and search for “WPS Push Button” option and just Tap on it.
Step 2: Now, Also Tap the “WPS” button on the backside of your Router. Within some seconds these both devices pair up and your device will connect to WiFi network. That’s It.
This method is very simple. Most of the router support option of WPS, if not then this trick will not gonna work. It’s a worth checking trick to connect to locked WiFi without Password. Please share how you like this article & also your valuable opinions and suggestions in comment section below. You would also like to know:
How to Kick Someone Off Your WIFI
Two Recommended Apps to Kick Someone Off Your WIFI
You are willing to put a hole in your pocket just to enjoy the fastest internet connection promised by your service provider. But it seems that you are not getting the value of your money because of slow connection. There are many factors that could affect your WIFI connection, but one of the things that you will definitely not want is wireless freeloaders. These are persons who will hitch on your network without permission and use your data for as long as they want.
How to Kick Someone Off Your WIFI
Change your passwords
Type your IP address in the address bar above the web interface of your internet connection and press enter.
If you are using MAC, you can find your IP address by opening the Apple Menu and then select “System Preferences”. You will see a Network icon, click this. You will find the word “Router”, and beside this word is your IP address.
For PC users, press the “Windows” and “R” keys at the same time. A command window will pop up, type “ipconfig” and press “Enter”. Look for the phrase “Default Gateway” and beside this is your IP address.
Once your wireless connection’s interface shows up, you need to access this by simply typing the admin username and password of your router. You can find this on your router’s sticker or you can call your internet service provider.
Upon entering the correct username and password, choose wireless settings and click “Change Password”. Enter your new password then turn your router off, then on again. This time, you will be the only one who can log-in on your connection.
Block unauthorized MAC address
Do you know how to kick someone off your WIFI by blocking unauthorized Mac address? Here are a few tips. Knowing your IP address is very important as you will need this to open your interface.
Again, if you are using MAC, you can find your IP address by opening the Apple Menu then select “System Preferences”. You will see a Network icon, click this. You will find the word “Router”, and beside this word is your IP address.
If you are using a PC, press the “Windows” and “R” keys at the same time. A command window will pop up, type “ipconfig” and press “Enter”. Look for the phrase “Default Gateway”, and beside this is your IP address.
Type this on the address bar above and press enter. Once you have gained full access to your wireless connection’s interface, you can check for uninvited guests depending on the manufacturer and model of your router.
Another tip is to check on your router’s LAN or DHCP settings, where you will find who else are connected on your WIFI including your own computer. Block unauthorized addresses on the “Security Settings” or “Firewall Settings”.
Call your ISP
Calling your ISP is another way. Before making a phone call, gather all the information you will need, like your account information and router’s model. Then c all and tell the customer service agent that someone’s been using your bandwidth without permission.
The agent can connect on your router to remove unauthorized connections if your router came from them. If your instinct tells you that somebody knows your password, you can request the customer service agent to create a new one for you.
You can also have your router settings updated. If you haven’t done this for a long time, then this might be the right time to do so. Ask the customer service agent to recommend the appropriate security settings for you and to update them as well. This is to prevent your wireless connection being used again by intruders.
Two Recommended Apps to Kick Someone Off Your WIFI
WIFIKill
How to kick someone off your WIFI? Use the app, WIFIKill, developed by Bartosz Ponurkiewicz. Some other applications may be helpful but are time-consuming. WIFIKill allows you to easily and quickly stop a freeloader from using your precious bandwidth. You will need a Nexus 7 or an android 4.0 or higher and a WIFIKill downloader app in order to install this on your device.
The good news is you can download the free version of the app, but the bad news is that you can only kick that someone off your WIFI for five minutes and there will be ads popping out with it.
You can also opt to the regular version which will cost you a few dollars but allow you to block those unwanted hoppers for an unlimited time, plus giving you an ad-free screen.
Once you have acquired the program, simply open it, and click “kill” beside the IP address of the intruder.
Netcut
This application is the same as WIFIKill. The only difference is that WIFIKill just requires you to have a phone but Netcut allows you to analyze, see and change the MAC addresses of those who are hopping on your internet.
So how to kick someone off your WIFI with Netcut? Just disconnect him or her on PC through this application. It is compatible to Widows 7, 8 and 8.1. But before going on with the steps on how to use Netcut, be reminded that this should not be used on public internet connections.
Using Netcut is very easy:
Simply download the program and install it on your PC. Just follow the prompts popping up on your web interface.
Once you have successfully installed the app, restart your PC and click on the Netcut icon.
Then you can see the list of all the devices connected to your WIFI and just simply click “cutoff” which is a button beside the device that you would like to disconnect.
You will see the blue button turn red which means it has lost its connection. Just click the”resume” button if you want to reconnect the device on your WIFI.
I’ve combined my former 3-part series of tips for network marketing success into a 1-stop resource you can use to move your business into a place where you say:
This industry isn’t hard. It’s just not simple.
There are mines to navigate. Do it right & you’ll succeed, converting as many MLM leads as you can handle into product sales and downline distributors.
Do it wrong and BOOM! It’s all over and you’re done 🙁
In this 3 part series each part will focus on one Mental idea & one Marketing idea.
Here’s what you’re going to learn over the next few minutes:
Feature Download: I’ve put together a free “Quick-Start Guide” that shows you how to implement the theory this post explains to you.
In this collection of MLM guides, you’re shown step-by-step how to get set up so you’re getting quality prospects for your network marketing business.
You’ll learn 5 Simple Steps to More MLM Leads: How to Recruit with the Push of a Button”, plus 5 Bonus Trainings that teach you:
- How to use Facebook
- How to use LinkedIn
- How to use the “Reverse Invite Method”
- The problem with social media for prospecting
- 3 strategies for more MLM leads
So you get more prospects WITHOUT the rejection.
Part 1: Self Control Is One Of The Most Vital Network Marketing Tips
The first Mental idea you must master is Self Control.
Napoleon Hill tells us in “The Law of Success In Sixteen Lessons” that
“All successful people grade high on self control! All ‘failures’ grade low, generally zero, on this important law of human conduct.”
Where can a lack of self control show up and damage your MLM business?
Jumping Ship
It’s absolutely amazing how many people in network marketing jump ship from “deal” to “deal”. One minute I see folks on social media promoting a company and then next month they’ve found the “next great thing”.
That’s a lack of self control.
People you look up to as successes in this industry got there because they drew a line in the sand. They chose their company and finally said,
“I’m in. I’m winning here, that’s it period!”
They probably said this in their 5th or 6th company, so don’t feel too bad…LOL
My point is that jumping from company to company is revealing your inability to exercise self control. Find where you “fit” and feel passionate and you work that opportunity until you succeed or die.
Misusing Social Media
Depending on how often you’re on my blog you may or may not know my stance on marketing.
I don’t promote offline marketing. Not because it doesn’t work but because it only works for a select few (those who come to the table with a warm market list that respects them…great examples are attorneys, doctors, established local businesspeople, etc).
I created an international downline by blogging after many years of struggling offline so it’s simply based on my own experience.
Actually, there were times during my struggles with the 3-foot rule, Starbucks 1on1’s, inviting folks to our Tues night Burbank CA opp meetings, etc when I saw some success & synergy.
The challenge for me was I still never enjoyed the actual activities…which I know is a key to working the Law of Attraction.
Personally, I LOVE performing the online strategies that work well, such as blogging, paid media, etc. Hey, if you love talking to one person for 90 minutes, go for it…I just know I can do a webinar & show 100 people my plan in the same 90 minutes.
Anyway, what I see happening on social media is networkers doing the same silly things they teach us to do offline.
Let’s go to Napoleon Hill again:
“One very common & destructive form of lack of self control is the habit of talking too much. People of wisdom, who know what they want & are bent on getting it guard their conversation carefully…It is nearly always more profitable to listen than it is to speak.”
When you go to Twitter, Instagram or Facebook and say things like, “I have the best opportunity in the world, come join me”, or “Our products are so awesome & we have a sale this month. Contact me to buy.”
It smacks of unprofessionalism, lack of self control, and is an example of bad social media use.
Worst of all, it doesn’t work. Does it? LOL
November 9, 2014 by Mitz
Hacking into your neighbor’s wifi network may be easier than you think—and, conversely, your neighbor may think it’s easy to hack into your network. Considering that the police are going to blame you for any activity which happens on your Internet connection, keeping wifi trespassers off your network is very important, so here are five ways to hack into a neighbor’s network that might be used against you.
Wifi Network Hack #1—The Open Network
In the early days of wifi, almost all networks were open networks—which meant any wireless device could connect to them. This was quite convenient, as no set up is required to connect to an open network so you could share your internet connection if required. Many routers even today come setup by default as open networks, so unless your neighbor has changed his settings, you may be able to immediately connect to his network. We might not want to hack into the neighbors internet, but sometimes it is there for the taking.
The only thing preventing someone from connecting to an open network is range—wifi routers typically have a range of only a few hundred feet (or less if too many walls are involved), so connecting to your neighbor’s network may be difficult in rural areas or some suburban areas when homes are far apart.
However, wifi hackers (sometimes called wardrivers) have long used directional antennas and signal amplifiers to overcome typical range limitations. Although a consumer laptop and a consumer wifi router have a maximum expected range of about 1,500 feet (500 meters), hackers can use special (but inexpensive) equipment to connect to networks up to 20 miles (30 kilometers) away. So even if you live in the wilds of Alaska, your neighbor might be able to hack your open wifi network.
Wifi Network Hack #2—Wireless Encryption Protocol (WEP)
When wifi routers first came out, manufacturers knew that some people would want security, so they added the Wireless Encryption Protocol (WEP) which was supposed to keep neighbors and other attackers out of your network. However, WEP was poorly designed and it turned out that anyone who could monitor your wireless communication for a few hours could break WEP.
Later, hackers discovered a way to send bad packets to your network that would make hacking WEP even faster—today, a hacker using a freeware program and a standard laptop can hack a WEP connection in two to five minutes.
WEP is still installed on the majority of routers, although it’s rarely enabled by default. On older routers, it may be the only security option. It’s better than an open connection, but it should not be considered actual security. (Use WPA2 instead if it’s available on your router.)
Wifi Network Hack #3—Wifi Protected Access (WPA) PINs
The replacement for WEP was WPA, which included several different protocols for extra flexibility. The two most commonly used protocols are WPA Pre-Shared Keys (PSK) and WPA push-button authentication. Both of these remain secure. However, a third protocol was the PIN method, where you would choose (or have chosen for you) a short number-only pin that you could enter into devices you wanted to connect to the network.
Hackers discovered they could brute-force the PIN—that is, they could simply try each combination one after another until they found the correct PIN for your network. The process might take from one minute to nearly an entire day, but eventually they’d get the right combination.
This is a perfect attack for a neighbor since he can run it for as long as it takes—he’s not going anywhere.
There’s no defense against the PIN attack except to make sure you disable PIN authentication on your wireless router. You can use the other WPA methods securely—but read the following section.
Wifi Network Hack #4—Weak WPA Pre-Shared Keys (PSKs)
Probably the most commonly-used wifi security method today, WPA-PSK (or WPA2-PSK) lets you enter a password on the Settings screen of your router and then enter that same password on your devices to allow them to securely connect to your wifi connection. This is easy and very secure—if you use a strong password.
Of course, if you’ve read the news lately, many people don’t use secure passwords. For example, one study found that nearly 50% of people used one of the top 100 passwords on a particular website—passwords like “password”, “password1”, “1234”, and so on. See these different ways obtain a WiFi password.
Known passwords and short passwords are called “weak passwords” in security research because they’re easy to break using the same brute-force method used against WPA PINS—basically an attacker keeps trying weak password after weak password until he finds your password.
Again, this is a perfect attack for a neighbor because he can use freeware software to run his computer 24/7 trying to break into your router. If you use a weak password, he will almost certainly succeed eventually.
The solution for this is simple: use a strong password—a password that’s is at least 8 characters, isn’t a word or name, and which includes some numbers or special characters. To allow me to use a strong password and not inconvenience guests, I have a sticky note on top of my router with my network password on it. This allows guests inside my home to simply walk up to the router and enter the password—but it prevents neighbors or anyone else from getting my password.
Wifi Network Hack #5—The Last Resort: Jamming
If you do everything right to secure your network, there’s nothing your neighbor can do to break your security—except convince you not to use it. Using a standard laptop or reprogrammable router, your neighbor can use a program that will jam your router any time you attempt to use a secure protocol. You won’t be able to tell that you’re being jammed, but you will notice that you either can’t connect to to your network any more or that it runs very slow.
If you stop using security and re-enable open networking, the jamming will stop, possibly leading you to believe that it’s your security that’s broken. In the mean time, your neighbor will be using your open wifi network.
The only defense against this is to have a radio communications expert diagnose your connection problem as jamming. Jamming—like all the hacks described here—is illegal, and if you demonstrate that you’re being jammed while a police officer watches, your neighbor will probably be fined. (Jail time for jamming is rare, but fines for jamming in the U.S. can be several hundred thousand dollars, making it one of the most expensive “minor” offenses.)
Conclusion
To improve your wireless network security, use WPA security with PSK and a strong password, or use WPA with push-button security. Remember to disable WEP and WPA-PIN, and if you have connection problems related to security, don’t take them at face value. Anything else may allow your neighbor to hack your wifi connection.
Our goal with Whereby is to create a browser-based video meeting tool with an emphasis on ease of use. Currently there are three different tiers of Whereby depending on your needs: Free, Pro, and Business. All versions of the Whereby allow for fast and easy video collaboration from anywhere in the world. Each plan has different features and limits, which you can learn about here.
Today, it takes an average of 7 minutes to get set up in a video meeting — and to us, that’s about 6 minutes and 45 seconds too long. Our goal is to keep you productive by striking a balance between simplicity, security, and quality in your video meetings.
To create a Whereby account, all you need is an email. After registering, you can create your own Room Link that you can manage as you’d like. Simply share the link with anyone you’d like to invite and start your meeting! After registering and signing in to your account, you’ll be able to go to Whereby to see your account home page. With an Whereby Pro account, this is where you’ll manage your rooms (up to 3).
If a colleague or client sent you a Whereby link over chat or email, you can either click on it to open a new tab, or copy and paste the link into your browser. Depending on the settings of the room, you may be prompted to “knock”, and they will allow you to enter the meeting. If it’s an open room, you will be brought straight into the meeting. If you’re charmed by how easy it is and want to set up your own meeting space to use in the future, you can register for a Free Whereby account.
In so many ways! We talk to our customers a lot, and are always uncovering interesting ways people use Whereby. Here’s just some of the ways we use our own product at Whereby…
Remote work: At Whereby, we want to get the best team members no matter their location, but this poses time and distance barriers for effective collaboration. To stay connected, our colleagues are a simple click away from one another over video. This also allows employees to be flexible around family and other life obligations, by being able to join the meeting from anywhere — even with our iOS app.
Stand-ups: Another way we stay connected is by having weekly or even daily stand-ups. These can be by department, project, or the entire company. With custom Whereby room links, you can have a designated room that you know is there and available every time you need it.
Externally: Internal video meetings are inherently easier than external — everyone is familiar or even standardized on the technology. When you go outside your workflow to meet with partners, customers, or prospective employees, that’s when confusion happens. Sometimes one needs to download an app, or runs into company permission issues, and you end up spending half your meeting trying to get into the meeting. This is where Whereby really shines; with no downloads and one-click-to-join in your browser, you can spend less time frustrated and more time meeting. Some recruiting agencies even conduct all their external interviews over Whereby!
We don’t require any downloads or logins to join, which is what makes Whereby unique from other video conferencing applications. Another way that we’re different from most is that Whereby meeting rooms are permanent links that you can go to at any time. Instead of creating a one time link, you can schedule a video meeting like you would schedule a normal in-person meeting. You can invite people into your room by sharing your room link, and they can join your room by pasting the link into any supported browser!
There’s language around video meetings that can be confusing at first, so here’s a brief word bank to get you started.
Room: A room has its own name, and a designated URL that creates a “space” or “room” for you to meet in. There are two different types of roles one can have when they join a room: Owner and Participant.
- Owner: The owner of a room is the person (and associated email) that has full control over that room. They can lock or unlock the room, kick users, and edit the background and logo (Whereby Pro only).
- Participant: A participant is someone who can join a room or attend a meeting. They don’t have administrative permissions, but they can still use features like Screen Sharing!
Capacity: Capacity is just like the capacity of a real room — only a certain amount of people are able to fit in the room. In our Free plan there is a capacity of 4 people. In our Pro plan there is a capacity of 12.
Lock/Unlock rooms: This feature is to make sure that only the right people are attending your meeting room. Before users are able to join, they need to request access to the room by Knocking (see more on this below). Only a Room Owner can Lock or Unlock their room.
Knocking: If a room is locked, people will need to “knock” to enter. Then the room owner will receive a notification that someone is knocking, and they will see a picture of the person trying to enter the room. Then the Room Owner can let the user in, or put them on hold if they aren’t quite ready.
Screen share: Any participant in a video meeting can share their screen. When you share your screen, all the participants in the meeting can see what you see on your device. Depending on the browser you’re using, you’ll see different options for screen sharing such as Sharing your Entire Screen, or a specific application window. For full details on screen sharing, check out our Support Center article here.
WebRTC: WebRTC stands for “Web real-time communication”, which is video from your web browser like Chrome, Safari, Firefox, etc.
I’ve combined my former 3-part series of tips for network marketing success into a 1-stop resource you can use to move your business into a place where you say:
This industry isn’t hard. It’s just not simple.
There are mines to navigate. Do it right & you’ll succeed, converting as many MLM leads as you can handle into product sales and downline distributors.
Do it wrong and BOOM! It’s all over and you’re done 🙁
In this 3 part series each part will focus on one Mental idea & one Marketing idea.
Here’s what you’re going to learn over the next few minutes:
Feature Download: I’ve put together a free “Quick-Start Guide” that shows you how to implement the theory this post explains to you.
In this collection of MLM guides, you’re shown step-by-step how to get set up so you’re getting quality prospects for your network marketing business.
You’ll learn 5 Simple Steps to More MLM Leads: How to Recruit with the Push of a Button”, plus 5 Bonus Trainings that teach you:
- How to use Facebook
- How to use LinkedIn
- How to use the “Reverse Invite Method”
- The problem with social media for prospecting
- 3 strategies for more MLM leads
So you get more prospects WITHOUT the rejection.
Part 1: Self Control Is One Of The Most Vital Network Marketing Tips
The first Mental idea you must master is Self Control.
Napoleon Hill tells us in “The Law of Success In Sixteen Lessons” that
“All successful people grade high on self control! All ‘failures’ grade low, generally zero, on this important law of human conduct.”
Where can a lack of self control show up and damage your MLM business?
Jumping Ship
It’s absolutely amazing how many people in network marketing jump ship from “deal” to “deal”. One minute I see folks on social media promoting a company and then next month they’ve found the “next great thing”.
That’s a lack of self control.
People you look up to as successes in this industry got there because they drew a line in the sand. They chose their company and finally said,
“I’m in. I’m winning here, that’s it period!”
They probably said this in their 5th or 6th company, so don’t feel too bad…LOL
My point is that jumping from company to company is revealing your inability to exercise self control. Find where you “fit” and feel passionate and you work that opportunity until you succeed or die.
Misusing Social Media
Depending on how often you’re on my blog you may or may not know my stance on marketing.
I don’t promote offline marketing. Not because it doesn’t work but because it only works for a select few (those who come to the table with a warm market list that respects them…great examples are attorneys, doctors, established local businesspeople, etc).
I created an international downline by blogging after many years of struggling offline so it’s simply based on my own experience.
Actually, there were times during my struggles with the 3-foot rule, Starbucks 1on1’s, inviting folks to our Tues night Burbank CA opp meetings, etc when I saw some success & synergy.
The challenge for me was I still never enjoyed the actual activities…which I know is a key to working the Law of Attraction.
Personally, I LOVE performing the online strategies that work well, such as blogging, paid media, etc. Hey, if you love talking to one person for 90 minutes, go for it…I just know I can do a webinar & show 100 people my plan in the same 90 minutes.
Anyway, what I see happening on social media is networkers doing the same silly things they teach us to do offline.
Let’s go to Napoleon Hill again:
“One very common & destructive form of lack of self control is the habit of talking too much. People of wisdom, who know what they want & are bent on getting it guard their conversation carefully…It is nearly always more profitable to listen than it is to speak.”
When you go to Twitter, Instagram or Facebook and say things like, “I have the best opportunity in the world, come join me”, or “Our products are so awesome & we have a sale this month. Contact me to buy.”
It smacks of unprofessionalism, lack of self control, and is an example of bad social media use.
Worst of all, it doesn’t work. Does it? LOL
Related Articles
- Taking Out Half-Walls
- How to Repair Interior Wall Cracks & Nail Pops
- How to Replace a 32-Inch Interior Door With a 36-Inch Door
- How to Frame an Inside Wall Against a Concrete Wall
- Making Two Rooms Into One
Walk into a variety of older homes and you’ll soon notice a curious thing: The older the home, the smaller the rooms and the more boxed-in the house plan feels. Of course you can’t totally eliminate a boxy effect — most homes are squares and so are the rooms, after all. In the past, small rooms were practical. Space heaters and fireplaces worked more efficiently in confined areas and unused rooms were simply closed off from the remainder of the house. At one time, a multitude of rooms also made the most of space for large families. Today, families are smaller but house and room size has grown. Beds, couches and furnishings are also larger as well. The result is a growing trend for large, open spaces and fewer separate rooms. To create the feeling in your own home, try knocking a wall or two out.
Shut off any possible circuits at the breaker panel or fuse box if there is any possibility there may be electrical wiring in the wall. If there are outlets or switches present, check them with a noncontact voltage meter before continuing.
Check the wall to determine if it is load-bearing. Clues that typically indicate a load-bearing wall include doubled top plates — the boards that run horizontally above the wall studs — as well as walls that run directly above or within a few inches of horizontally running beams or walls. Load-bearing walls are typically near the center of the house and run for most of the house length or width. Consult a structural engineer if you have any doubts, as removing a load-bearing wall improperly can cause serious damage to the house.
Look for evidence of electrical wiring, heating and air vents or plumbing pipes running through the wall. Take note of any light switches, electrical outlets, wired objects such as electric smoke detectors or furnace thermostats, or heating and air vents. Move to the attic or basement, as applicable, and check for anything running into the wall. Even in the absence of visible evidence of these objects, the wall may still contain them. Proceed carefully, or reroute items as needed. Consult a professional for further assistance.
Spread a sheet, an old blanket, or enough cardboard or newspaper to protect your floor during the wall demolition and removal. Remove or cover nearby furniture and pull down any wall furnishings to prepare the area.
Remove the wall sheathing. If you have any doubt that the wall may contain wiring, pipes or ducts, cut or poke a peep hole in the wall first and peer in with a light and mirror if needed. Attack the sheathing depending on the type and your preferences. You can use a hammer or sledgehammer to simply knock out drywall or slice through it with a utility knife along the joints and pry up chunks. Paneling pries up easily. Work carefully, alert for hidden surprises.
Tear out the studs running vertically through the wall. Slice through each stud somewhere near the middle, using a reciprocating saw or similar tool. Grasp each stud end, one at a time, and twist, pull and work the stud free. Typically nailed twice on either end, the studs will be stubborn but they will come free. Use a hammer, sledgehammer or pry bar to encourage a stud to work loose.
Wedge a pry bar between the top plate and ceiling. Pull down, pull the bar free and reinsert several inches away. Continue down the board’s length, loosening the board little by little. Move to the center and pull again, if the plate is still attached, and wrench it free with the pry bar. Repeat with the floor plate, prying between the floor and the remaining plate.
Touch up the ceiling and walls, wherever the wall was positioned, to remove any indicator that the wall existed. Use joint compound to smooth out rough surfaces, spreading it lightly across the defect and sanding it smooth, then applying another layer feathered out past the first and repeating. Finish with a coat of primer then paint. Repair other surfaces as applicable or renovate all the wall surfaces at once. After cleaning up the demolition mess, fix the floor where the wall ran, as needed.